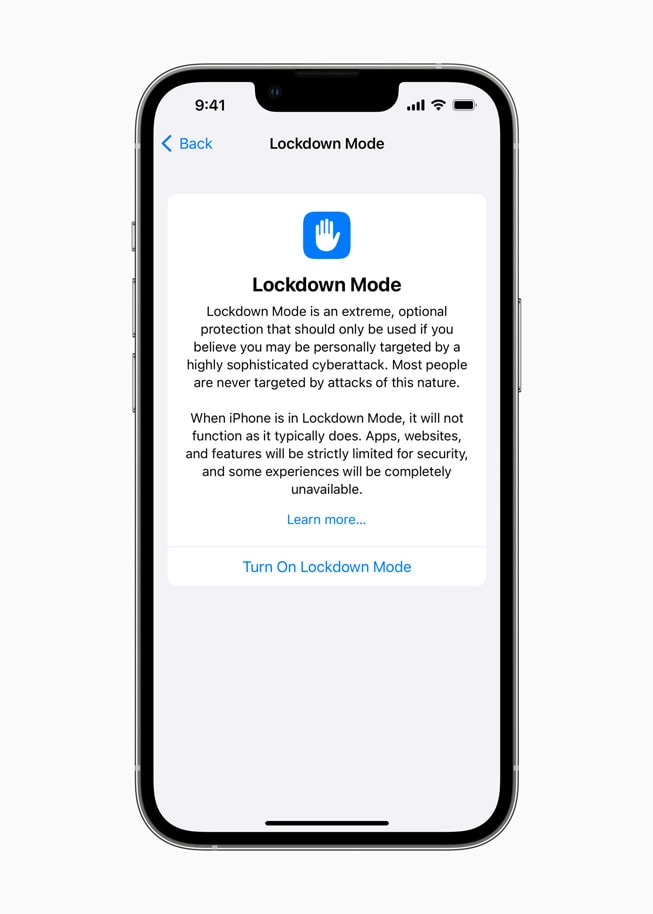
We tell you everything we know about Apple’s ‘Lockdown Mode’
Apple has announced initiatives aimed at users who are personally attacked by sophisticated cyber threats, including Lockdown Mode, a protection or isolation mode. This is the first functionality of itsRead More →