The developers of L0phtCrack, a popular digital forensics and password recovery tool, have announced that this will become an open source project and will be maintained in collaboration with other developers.
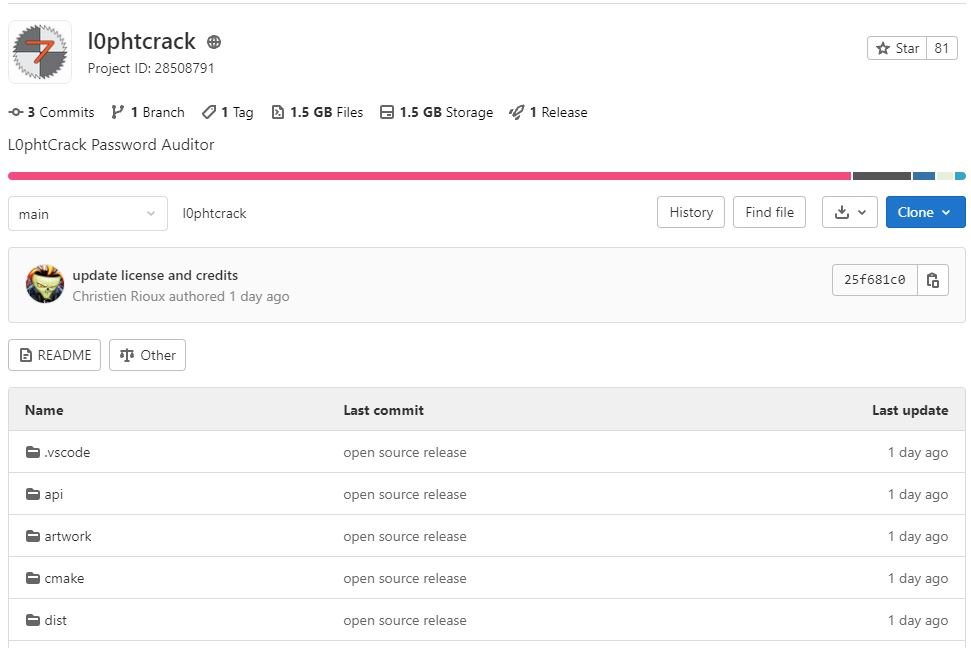
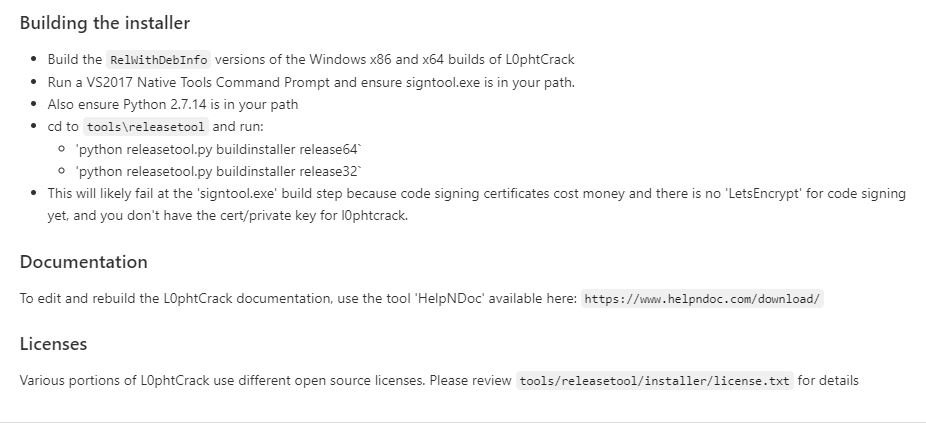
According to the experts in digital forensics of the International Institute of Cyber Security (IICS), this tool is functional for the deployment of some security tests on Windows systems and password recovery using dictionary tactics, brute force attacks and other methods. The tool is available in GitLab and has all kinds of backup material to understand how it works and use it without setbacks.
As some users will recall, dictionary and brute force attacks are the most commonly used methods to find passwords, used by both digital forensics experts and threat actors to recover the security keys of certain systems.
L0phtCrack, also known as Mudge, was developed by a group of hacking specialists and subsequently acquired by security firm Zatko, although it was also operated by Symantec between 2004 and 2009.
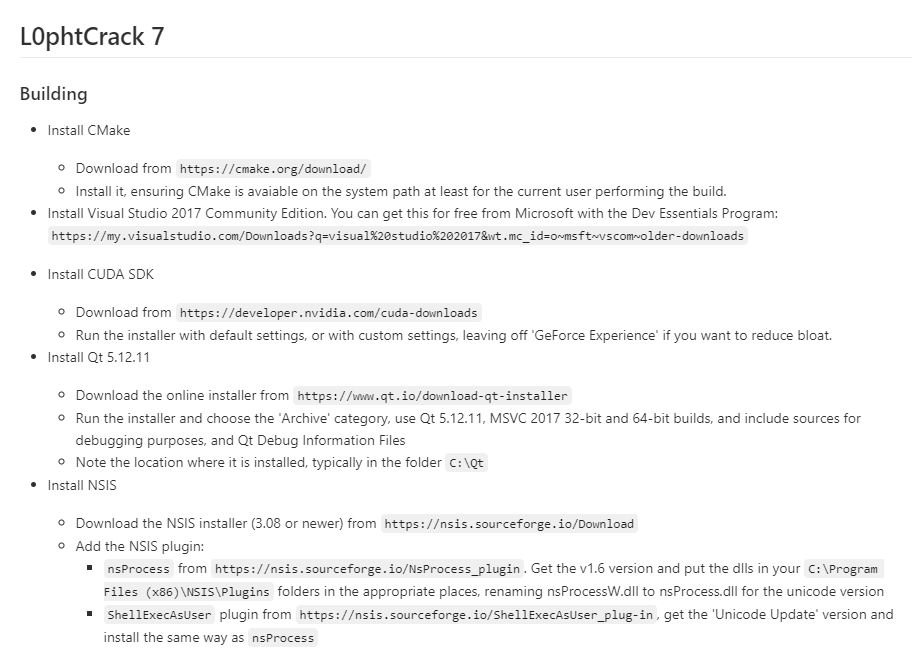
Current developers are reportedly exploring the world of open source and other potential options for software development in the coming years. The full transfer to open source will take some time, as there are commercially licensed libraries built into the product that need to be removed or replaced.
Moreover, digital forensics experts mention that activation for existing licenses has been re-enabled and should work as expected until an open source version can be made available.
This weekend, the availability of L0phtCrack open source, specifically version 7.2.0, was officially announced. The developers recommend users interested in maintaining the project to contact the developers and find the best way to collaborate for the maintenance of this project.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
