Symantec researchers discovered a new malicious operation using cryptocurrency malware identified as Clipminer. This strain would be based on the KryptoCibule malware, a Trojan with cryptocurrency and e-wallet theft capabilities, and up to 4,370 cryptocurrency addresses possibly related to this campaign have already been identified.
The attack begins by delivering the malicious payload in the form of a WinRAR file capable of being automatically extracted to start a file .CPL that downloads a DLL library. This DLL creates a new registry value and is located in C:\Windows\Temp\ to profile the host and download and install the Clipminer payload using Tor.
Subsequently, the ID of the affected system is sent to the attackers’ C&C server, receiving in return a payload that will be installed in C:\ProgramData\ or C:\Program Files (x86)\. Once it runs, Clipminer will create scheduled tasks for persistence and create an empty registry key, probably as a method of identifying hosts that have already been infected.
When this file has been received, the payload starts an Onion v3 service with a unique address and monitors all keyboard and mouse movements on the affected machine, as well as verifying the processes of any security tool running in the background. As if that were not enough, when Clipminer does not detect user activity, an XMRig Monero miner configured to use all CPU threads is started without risk of the affected user experiencing a noticeable drop in the performance of their machine.
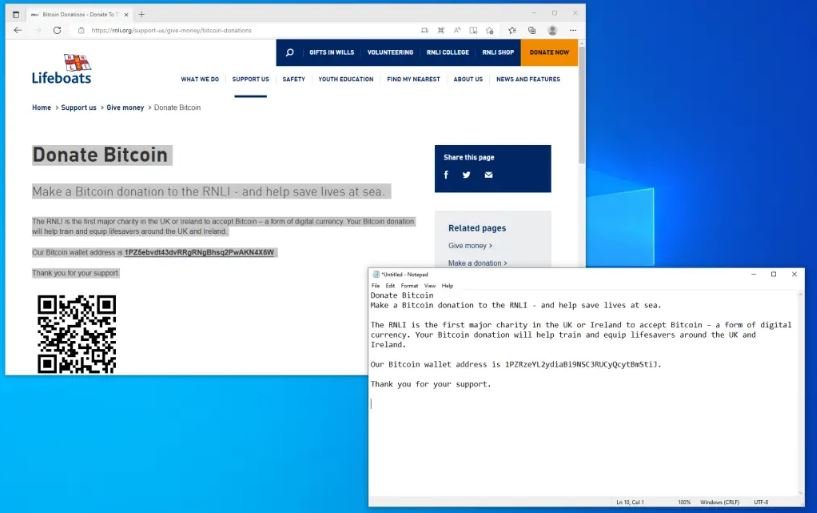
The malware can deploy all the tasks described above while monitoring the clipboard tools, waiting for the user to enter any sequence of characters similar to a cryptocurrency address; if Clipminer detects this, it will delete the legitimate information on the clipboard to replace it with a cryptocurrency address belonging to the hackers.
This malware variant has been rapidly distributed for a couple of months now, using alleged hacked software available on P2P networks, torrent platforms, and links in YouTube descriptions. As with any malware variant that employs similar distribution mechanisms, users are advised to try to avoid downloading pirated software, as this has always been one of the most efficient methods of spreading computer viruses.
Cryptocurrency enthusiasts are advised to store their wallets’ information properly, using security tools such as password generators and malware scanners.
Feel free to access the International Institute of Cyber Security (IICS) websites to learn more about information security risks, malware variants, vulnerabilities, and information technologies.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
