A few weeks ago, the WordFence Threat Intelligence team discovered a security flaw in Site Kite by Google, a WordPress plugin that is present on about 300,000 websites. The vulnerability allows any authenticated user with minimal privileges to become the owner of the Google Search Console for any site running the compromised plugin. The vulnerability was reported to Google on April 21 and corrected on May 7, 2020.
The vulnerability is considered a critical security issue, as its exploitation could allow hackers to gain full access to the victim’s resources. Owner access allows threat actors to modify the website map, delete result pages in the Internet search engine, and even facilitate the deployment of malicious SEO campaigns.
To mitigate the risk of exploitation, experts strongly recommend upgrading to the latest version (v1.8.0) of Site Kite immediately.
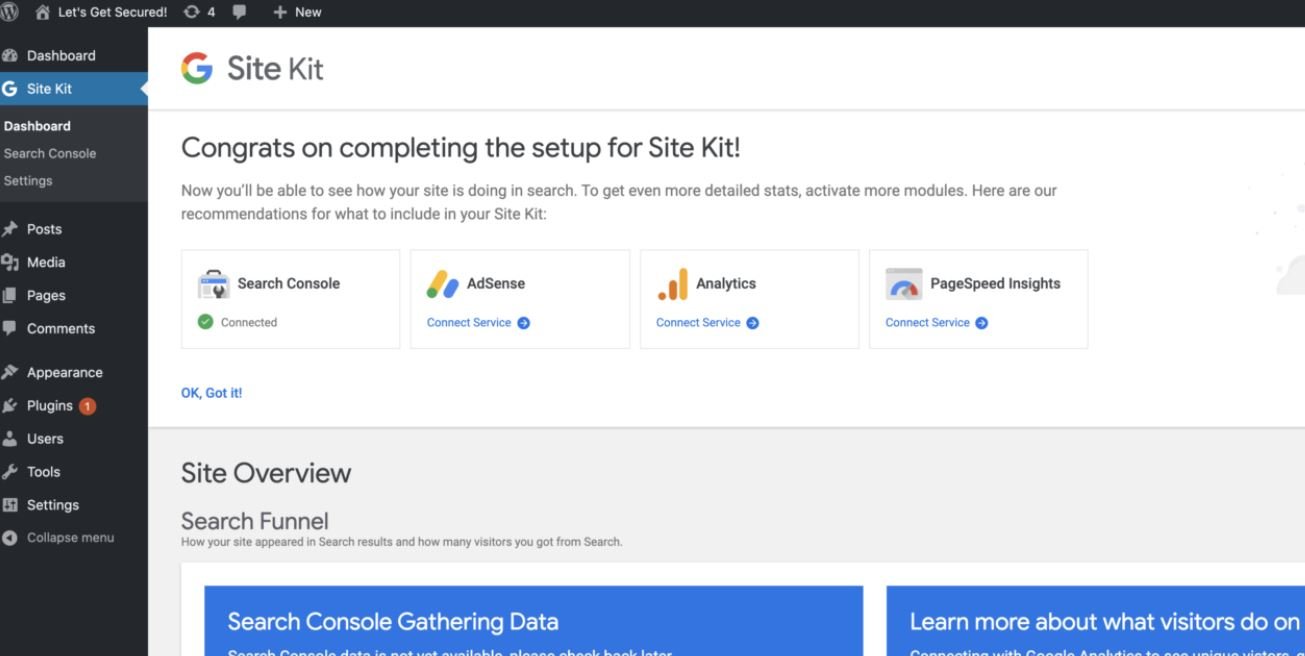
This plugin is used to obtain and display information about website visitors and the performance of results in the search engine. This is done by connecting to a Google Search Console account and providing additional capabilities to connect to Analytics, AdSense, PageSpeed Insights, Optimize, and Tag Manager.
To establish the first connection to Site Kit and Google Search Console, the plugin generates a proxySetupURL that is used to redirect a site administrator to Google OAuth and run the site owner verification process through a proxy.
Due to the absence of checks in the admin_enqueue_scripts action, the proxySetupURL is displayed with the naked eye as part of the HTML source code of the management pages to any authenticated user accessing the /wp-admin panel. To be more specific, the admin_enqueue_scripts action activates the enqueue_minimal_admin_script function, which queues the googlesitekit-base set and finally includes googlesitekit-base-data, which returns the online database data. This includes the proxySetupURL.
This allows subscriber-level users to become Google Search Console owners anywhere affected.
When a new owner is set up for Google Search Console, an email is sent mentioning, “Owners can change critical settings that affect how Google Search interacts with your site or app”. A hacker could take advantage of this situation, deploying malicious SEO campaigns, using console access to inject malicious content for monetization purposes on the affected site, among other risky scenarios.
The vulnerability received a score of 9.1/10 on the Common Vulnerability Scoring System (CVSS) scale, although it has not been assigned an identification key.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
