Cybersecurity specialists report the detection of a denial of service (DoS) botnet that has grown excessively in recent months, attacking the Russian technology giant Yandex with more than 21 million junk requests per second. The botnet was identified as Mēris and derives its power from tens of thousands of compromised devices, mainly powerful networking equipment.
During this week several Russian media reported that Yandex suffered a powerful DoS attack, described as the most powerful incident ever detected in its kind. Details have emerged today in a joint investigation by Yandex and Qrator Labs firm offering DoS protection services.
Information gathered during some attacks deployed by the Mēris botnet (Latvian term for “plague”) reveals that this malicious development has around 30,000 compromised devices.
The attacks against Yandex’s servers were based on some 56,000 malicious hosts, although researchers believe the number of compromised devices may exceed 250,000.
According to the Qrator Labs report, the difference between the attacking force and the total number of infected hosts that make up Mēris is explained by the fact that administrators do not want to exhibit the full power of their botnet. The researchers note that the compromised hosts in Mēris are high-capacity devices that require an Ethernet connection.
Mēris is the same botnet responsible for generating the largest volume of attack traffic that Cloudflare recorded and mitigated to date, as it peaked at 17 million requests per second. However, the Mēris botnet broke that record during the attack on Yandex, as its flow on September 5 reached a force of 21 million RPS.
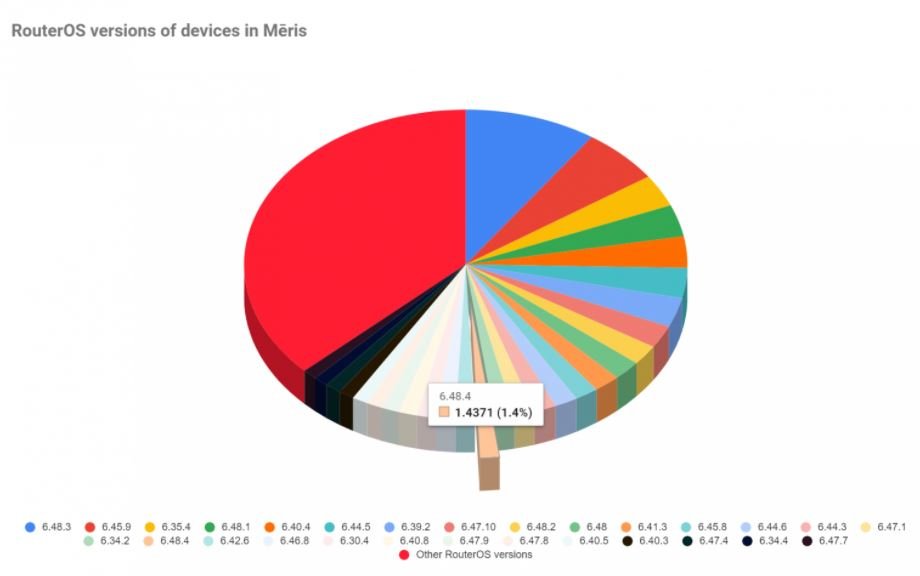
To implement an attack, Mēris is likely to base itself on the SOCKS4 proxy on the compromised device, using the HTTP pipelining DoS technique and port 5678. As for the compromised devices used, the researchers say they are related to MikroTik, a company that makes networking equipment for all kinds of companies.
Most of the attacking devices had 2000 and 5678 open ports. The latter targets the MikroTik team, which uses it for the neighbor discovery function. The researchers found that while MikroTik provides its standard service through User Datagram Protocol (UDP), compromised devices also have a Transmission Control Protocol (TCP).
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
