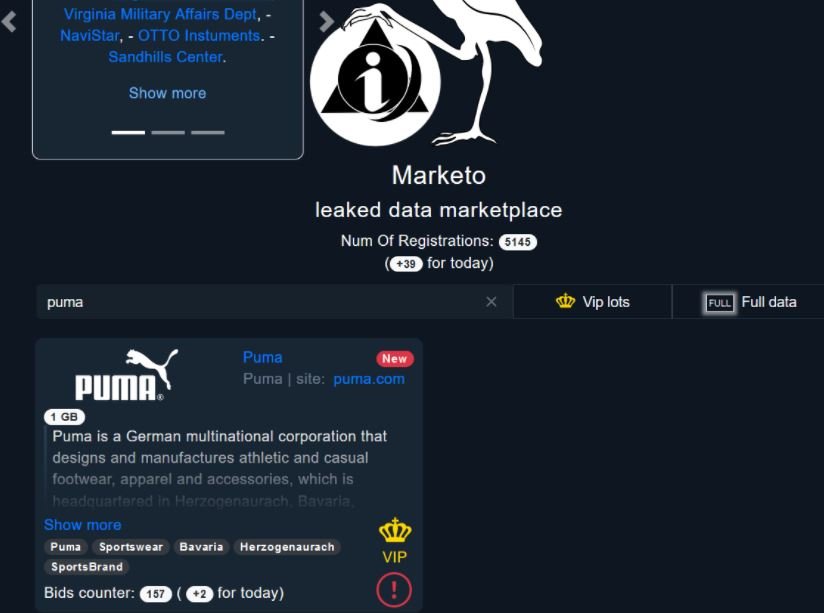
Through an advertisement on Marketo, an illegal platform on the Tor network for the purchase and sale of stolen information, an alleged leak obtained from Puma, one of the most recognized sportswear manufacturers in the world, was revealed. According to Security Affairs researchers, the publication points out that the threat actors stole more than 1 GB of confidential information, which will be offered to the highest bidder on this illegal platform.
Apparently, this operation is specifically dedicated to the theft and sale of confidential information, so researchers rule out that this is some offshoot of a ransomware group. It should be remembered that some ransomware operations are also engaged in the theft of confidential information for extortion purposes against victims.
To demonstrate the legitimacy of the leak, threat actors released some samples of the compromised information, which apparently includes snippets of source code and other details linked to Puma’s management systems.
Although the threat actors did not provide further details about this leak, experts who have analyzed the code leaked by the hackers mention that this information could have been obtained as a result of a security incident impacting an external service provider.
About Marketo, the researchers point out that this is a newly created platform and that it is characterized mainly because it allows interested parties to bid to acquire the stolen information. At the time of writing, 157 Marketo users had bid to gain access to this data.
Experts claim that if a sophisticated malicious hacker gains access to this information, they could deploy subsequent attacks and generate highly considerable damage. So far, Puma has not commented on the matter.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
