Ethical hacking is a field in constant evolution, so it is necessary that researchers are always informed about the latest trends in terms of tactics, hacking groups and security tools. The use of the best hacking tools is fundamental in the most important cybersecurity investigations today, since they are the resources used by researchers in events such as Black Hat, Pwn2Own and DEF CON.
This time, the experts in ethical hacking from the International Institute of Cyber Security (IICS) will show you the 10 best hacking and cybersecurity tools, all used by the most recognized researchers during 2021. Before proceeding, we remind you that this article was prepared for informational purposes and is not a call to action; IICS is not responsible for the misuse that may occur to the information contained herein.
TruffleHog
This is a recently released Chrome browser extension that features a feature to remove lost credentials and security keys that have been incorporated into JavaScript code by mistake.
According to ethical hacking experts, TruffleHog is the best way to find API keys for software-as-a-service (SaaS) providers and cloud services, which can prevent severe security incidents.
Truffle’s developers mention that permissive Cross-Origin Resource Sharing (CORS) configurations on platforms such as Amazon Web Services (AWS) are the main cause of credential leakage. This tool will avoid most of these issues, allowing developers to get on with their work without worrying about credential exposure.
Raider
Ethical hacking experts describe Raider as a utility for testing security in web application authentication mechanisms. The developers of Raider claim that this framework covers any security breaches left by existing vulnerability scanning tools.
Raider is Python-based and tracks client status while offering an interface to handle elements important to the authentication process, including headers, cookies, and user tokens.
Enfilade
Enfilade allows administrators of MongoDB instances exposed on the Internet to scan their resources for some of the most common malware variants. Developed by researcher Aditya K. Sood, this utility also offers comprehensive database analysis looking for indicators of compromise.
Other features of the tool include access verification to detect potential user enumeration attacks and remote code execution, plus it is compatible with virtually all currently active mongoDB versions.
The abuse of vulnerabilities in databases is a very common cybercriminal behavior today, so the existence of tools like Enfilade is vital for the world of ethical hacking.
WARCannon
This is a platform for non-invasively analyzing regular expression patterns across the Internet and comparing them with corresponding vulnerability indicators. In other words, WARCannon offers a means to look for flaws in web applications, frameworks, and open source components.
According to ethical hacking experts, this process requires big data management on a scale never seen before, although WARCannon’s architecture makes what would be an unviable project materialize and become affordable.
Scrapesy
Scrapesy was released during the most recent edition of Black Hat and is described as a tool to scour the conventional web and dark web to find user credentials exposed in security incidents.
The utility was developed by Standard Industries and released as open source software. Its developers claim that Scrapesty is designed to speed up the process of responding to incidents after a data breach.
Hopper
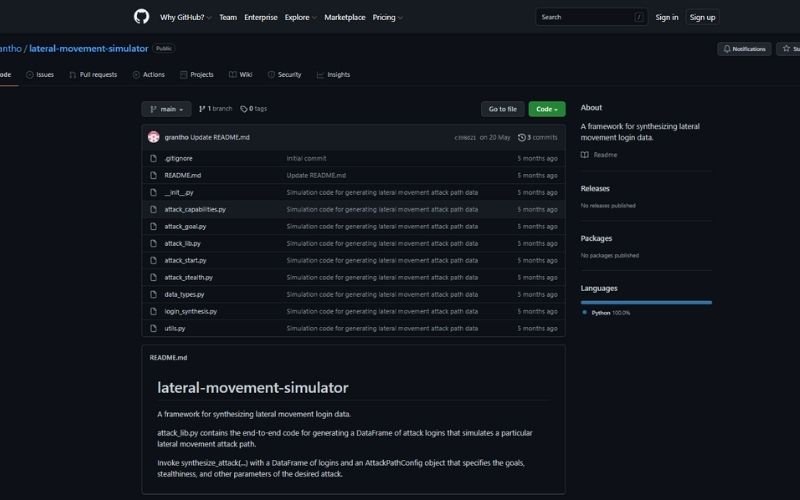
This is a tool designed to analyze a machine learning process in order to detect sideways motion attacks, although ethical hacking experts point out that this is not its only function. As some users will recall, lateral movement is the process by which hackers exploit various vulnerabilities to gain an entry point into a specific network, gaining access to all the resources stored there.
Hopper looks for indicators of lateral motion attack compromise, which will allow researchers to determine which activities warrant additional action in order to contain the threat.
USBsamurai
Air-gap systems can be very vulnerable to attacks with local access, such as a malicious USB cable attack for example. USBsamurai can contain this kind of threat using only a cable, a unifying dongle and a USB radio transceiver with open source features and design, ethical hacking experts say.
In the words of its creators, USBsamurai employs “a patented wireless protocol that is not detected by WiFi mechanisms, which makes it suitable for pentesting tasks and other security tests.”
Reconky
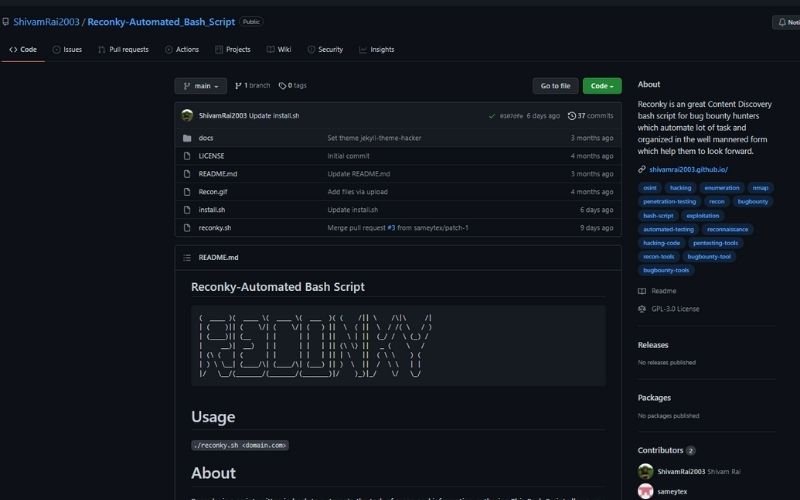
This tool is capable of automating tasks of recognition and collection of information, mention experts in ethical hacking. Reconky allows researchers and vulnerability bounty hunters to conduct a refined search for the best detection of potential security flaws.
GoKart

This is a security scanner for applications developed in the Go programming language created as an open source project by the security firm Praetorian.
Filesec.io
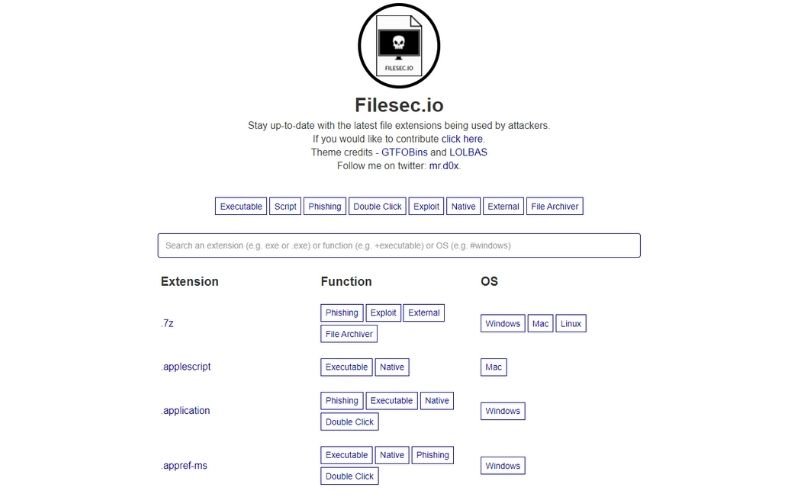
Ethical hacking experts will find in this utility a repository of file extensions that can be used for malicious purposes, which could prove useful at various times of pentesting and other security tests.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
