It is nothing new that source code repositories are used to host sensitive information of an organization such as access credentials, personal data, among other records, which can be attractive to threat actors always looking for vulnerable data.
One of the most important efforts to prevent these incidents comes from the telecommunications firm Twilio, whose developers have released a free tool to prevent developers from accidentally adding potentially confidential files to code repositories.
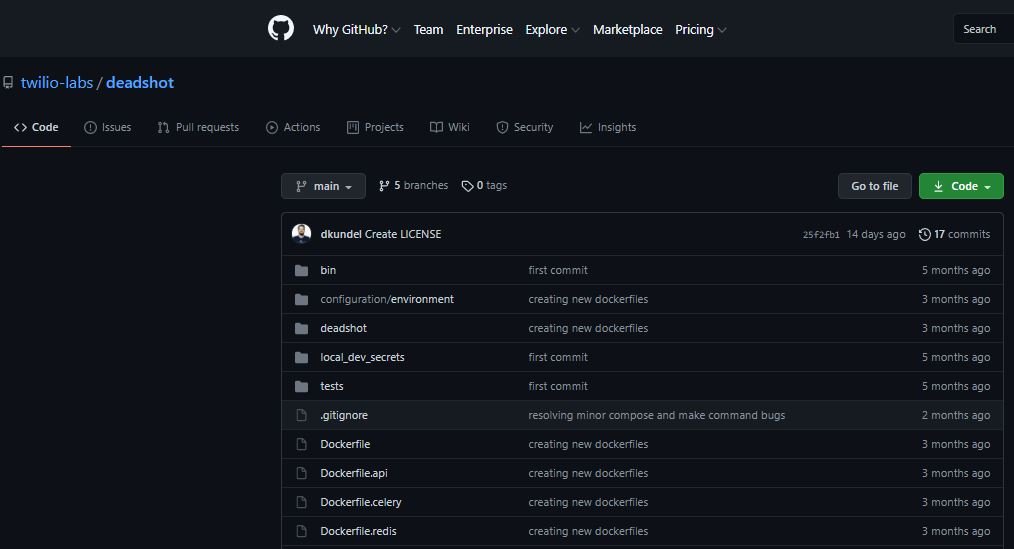
Dubbed “Deadshot”, this tool is capable of monitoring pull requests on GitHub in real time, as well as identifying the possible inclusion of sensitive information in any code sample. Laxman Eppalagudem, software engineer responsible for this project, mentions that it is practically impossible to manually monitor all the code uploaded to these platforms, so Twilio experts began the development of a functional tool for these cases.
“This tool works with the approach known as ‘implement and forget’; as it runs on each commit, Deadshot must alert project owners before any traces of potentially sensitive information leave the organization’s infrastructure. Developers can specify what kind of information they want to monitor with Deadshot, which will allow them to receive alerts in case of possible leak.”
Deadshot’s release is backed up by a thorough investigation by Twilio’s security teams: “We have found that most incidents involving sensitive information exposed in repositories are linked to oversights on development teams; the tool will provide an additional layer of security to prevent the exposure of corporate secrets and improve practices in the software development industry,” says Yashvier Kosaraju, product security manager at Twilio.
Kosaraju added that Deadshot has been designed so that only administrators of the organization can install it on Github accounts, which they hope will significantly reduce the danger of hacking linked to the tool: “Other scripts and bots that perform this type of scanning on GitHub and other code repositories are already well established on the offensive side, so the use of Deadshot will be solely for security purposes.”
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
