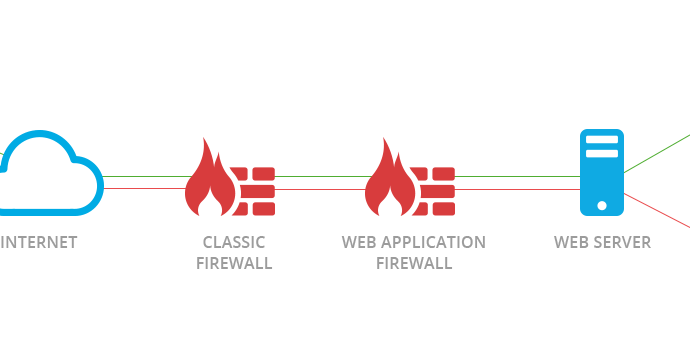
Hack networks via Fortinet FortiNAC by sending specially crafted requests to the tcp/1050 service
This problem arises as the importance of cybersecurity around the globe continues to grow. The security architecture of our network is under continual attack, and it is becoming more vitalRead More →