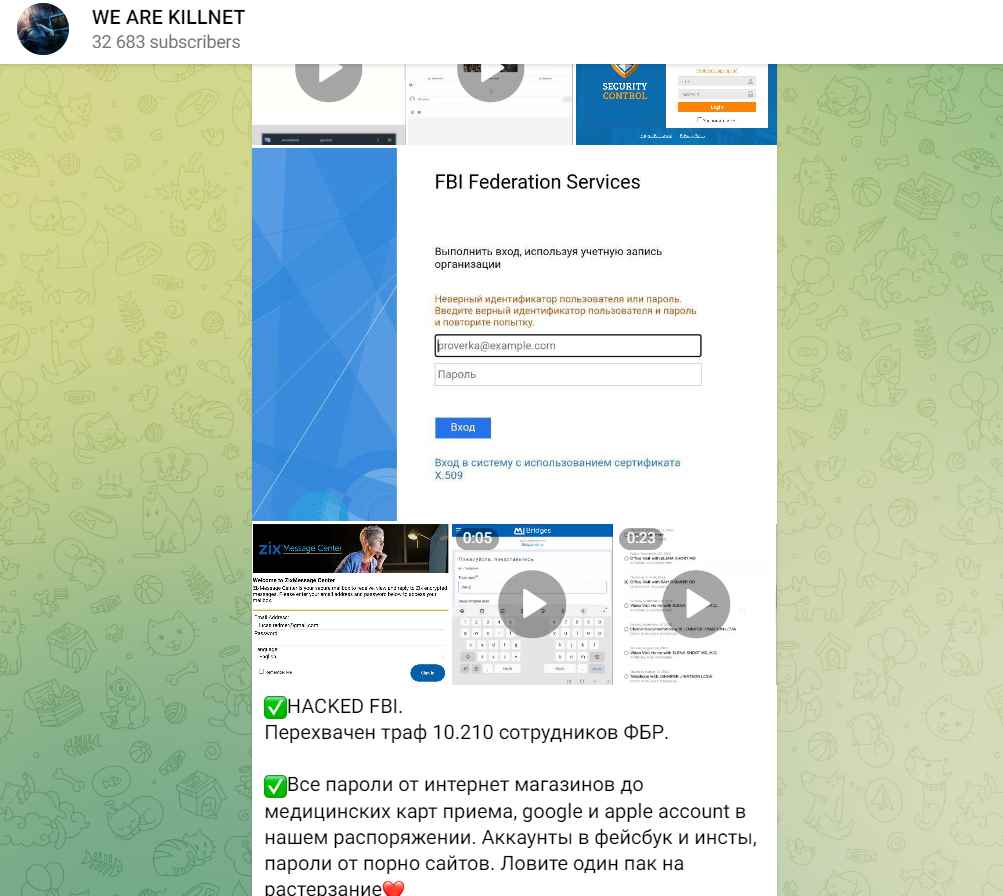
KillNet, a Russian hacker organization leaks personal data 10,000 FBI officers
KillNet, a Russian hacker organization, has made the assertion that it breached the FBI’s database and stole the personal information of more than 10,000 US federal officers. This purported assault,Read More →