Although sometimes the concept has a negative connotation, hacking can be very useful for totally legitimate purposes in various fields, including the use of smart devices. According to mobile hacking experts, this practice is just the search for ingenious ways to access hidden features on a device.
On this occasion, specialists from the International Institute of Cyber Security (IICS) will show you the best mobile hacking tools for Android devices currently available. While some of these apps require a subscription or a rooted device, they are really useful in hacking tasks for smart devices.
Before proceeding, as usual we remind you that this article was prepared for informational purposes only and should not be taken as a call to action. IICS is not responsible for the misuse that may be given to these tools.
AndroRAT
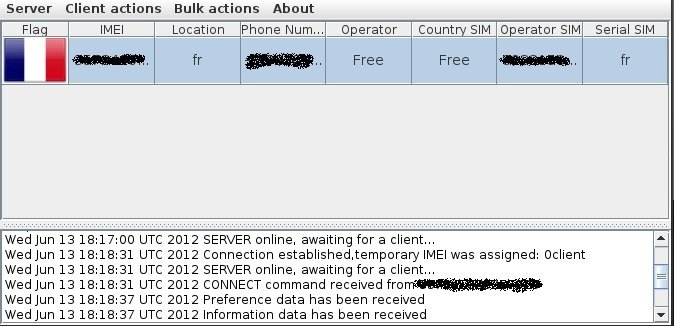
This is an open source and free Java client/server application that was developed by a team of 4 researchers as part of a university remote control project on Android systems for information extraction.
According to mobile hacking experts, among the main functions of AndroRAT is the extraction of call history, contact lists, SMS messages, location details and even some image and video files.
Fing
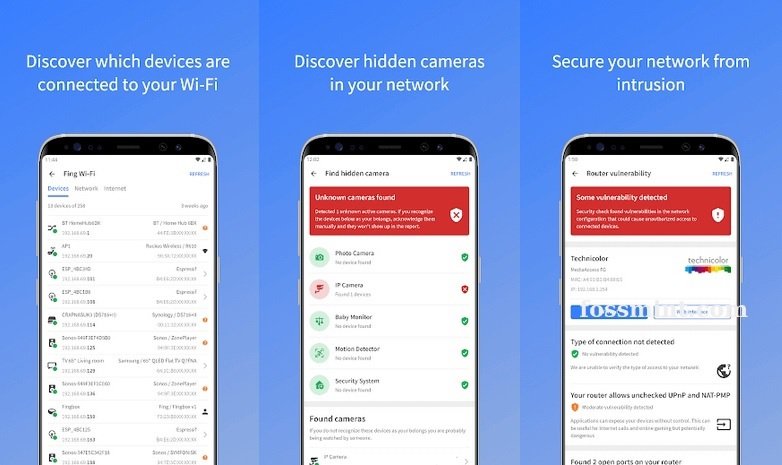
This is a network scanner that helps detect and identify all devices connected to a WiFi point, in addition to analyzing potential vulnerabilities in a router.
This tool has a free version that allows you to collect some general details about these connections, such as bandwidth usage, blocking potential intruders and setting parental controls. By accessing the Premium version, users will be able to have advanced features.
Nmap
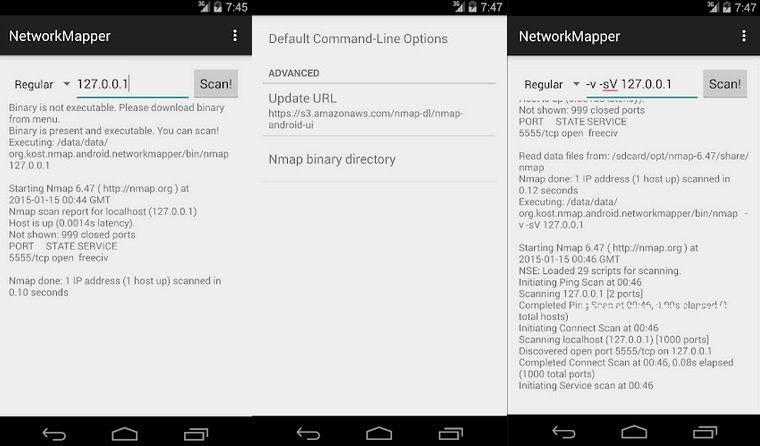
Also known as Network Mapper, this is an unofficial free Android client of the popular Nmap scanner that allows you to identify hosts, protocols, open ports and services, as well as their network configuration and vulnerabilities.
Although Nmap has a version for non-rooted devices, it does not receive constant updates, so it is probably best to use the version for rooted devices.
NetX Network Tools PRO
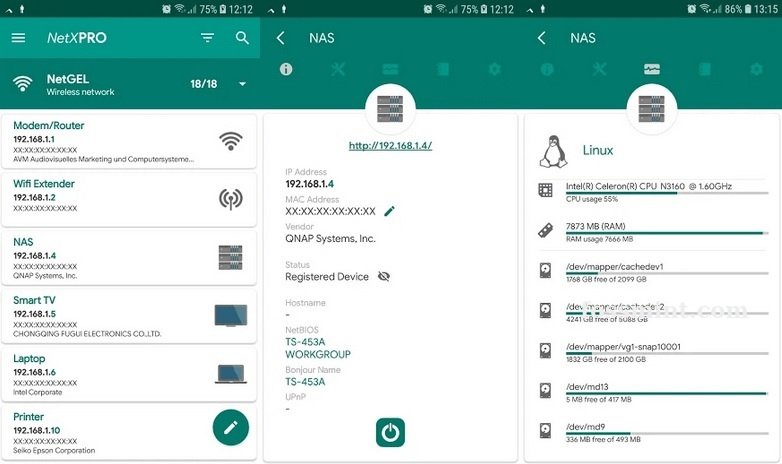
NetX is a paid network analysis tool for extracting data such as IP addresses, MAC addresses, NetBIOS names, mobile network signal strength and gateway, among other records, mobile hacking experts say.
This program has a built-in Secure SHell (SSH) client for running remote tasks, plus multiple features that are not available on most of its counterparts. This tool is available for only $3 USD.
zANTI Mobile Penetration Testing Tool

This is considered as one of the most popular mobile hacking applications, as it allows identify and simulate mobile attack methods and real exploits.
Users can use zANTI for information gathering tasks about any connected device or network. Although you can use this app on non rooted devices, you will need root access to use the advanced features.
PortDroid – Network Analysis Kit & Port Scanner
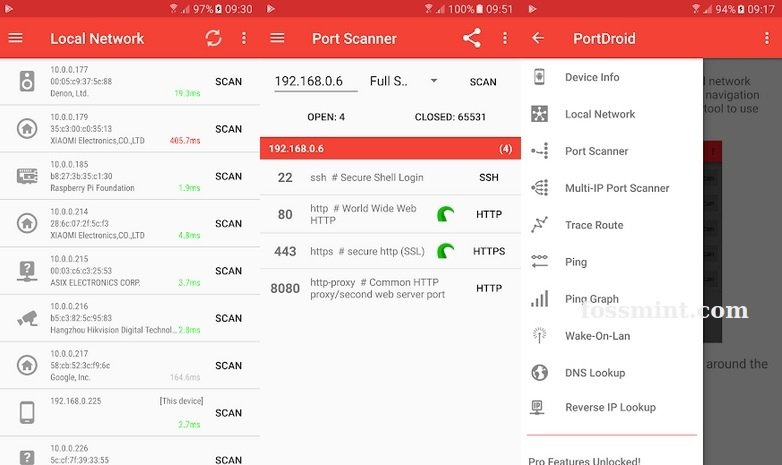
This is a network analysis app for network administrators, pentesters, and mobile hacking experts who require extra help as it includes features like ping, traceroute, DNS lookup, reverse IP, and port scanning.
Sniffer Wicap 2 Pro
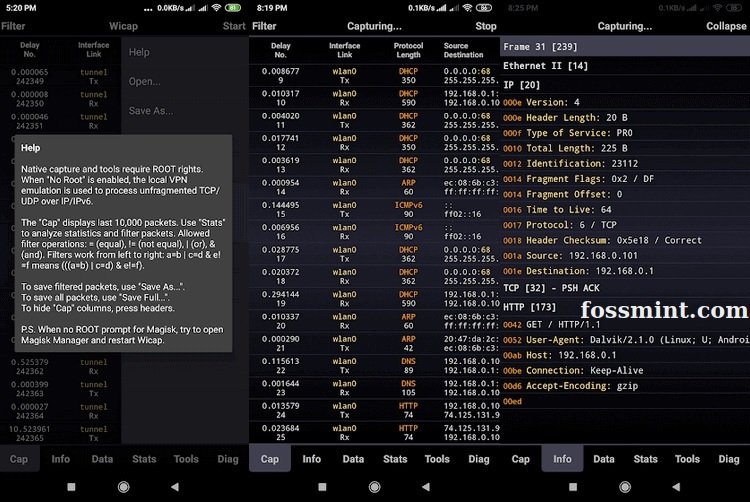
This is a packet tracker for WiFi and LTE networks, with a modern and easy-to-use user interface. While it is a great option for mobile hacking, its cost of $8 USD can lead those interested to look for more accessible options.
Hackode
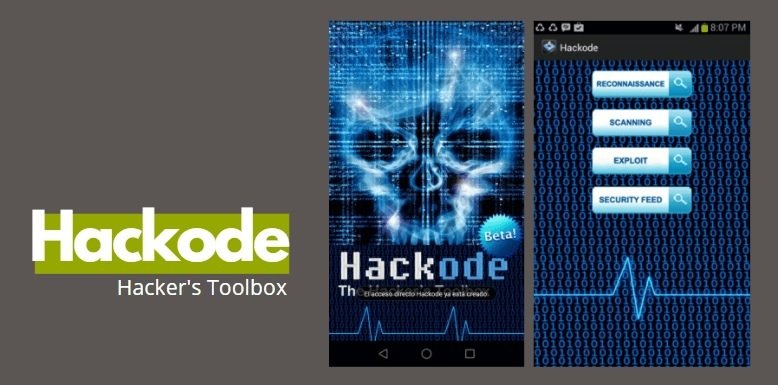
This is another web-based application full of useful and functional tools. Hackode is intended for cybersecurity experts and network administrators, although it also includes other functions.
This tool allows you to perform port scans, ping, crawl, IP lookup and access to Mail Exchange logs, plus it is distributed for free and works on non rooted devices.
cSploit
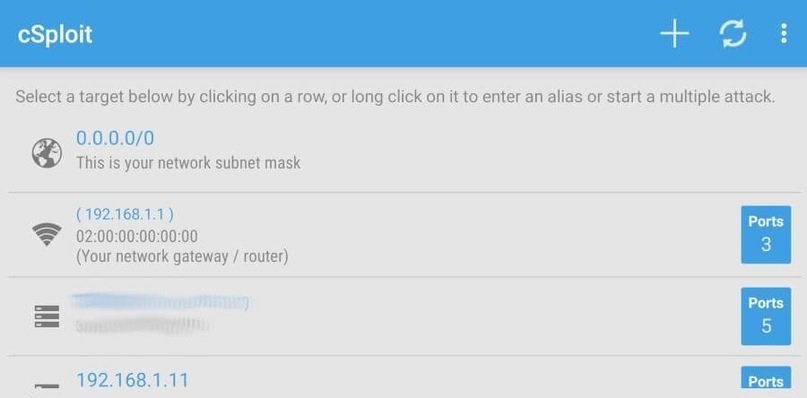
This is a network analytics and penetration suite designed to provide advanced tools for cybersecurity experts who are mobile hacking enthusiasts. Highlights of this tool include local location mapping, built-in tracking, TCP/UDP packet spoofing, JavaScript code injection, password tracking, session hijacking, and DNS spoofing, among others.
DroidSheep
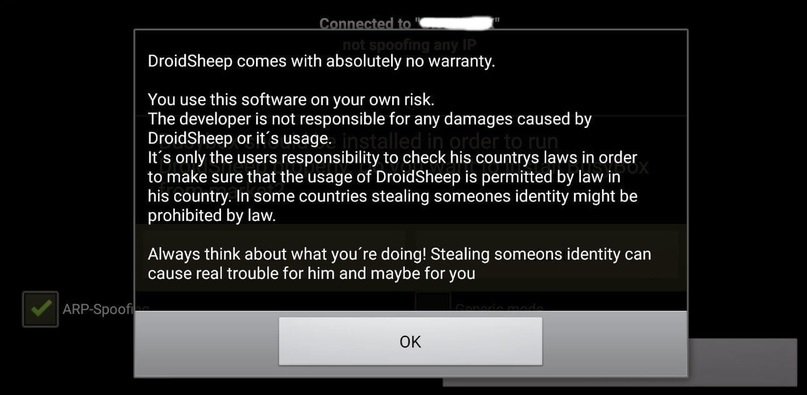
This is a WiFi network tracker capable of intercepting insecure sessions in web browsers. DroidSheep was designed to test and simulate threats, find network vulnerabilities, and mitigate the effects of real cyberattacks.
This is a free and open source tool and although it is very easy to install, it requires a rooted device.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
