The Russian military invasion at Ukraine has generated repercussions in multiple fields, including the world of cybersecurity. Public and private organizations in Russia and Ukraine have been the target of all kinds of cyberattacks over the past week, creating new challenges for system administrators.
A report by Cisco Talos researchers points to the detection of a cybercriminal group trying to trick individual users who are looking for hacking tools for the deployment of their own attacks. Attackers publish tools and advertise them as ways to attack Russian or pro-Russian websites, quickly spreading the threat.
Open source repositories are full of tools related to the terms “Russia” and “Ukraine,” most designed for the deployment of denial of service (DoS) attacks. As anyone might guess, the installation of these tools carries a security risk, as there is no way to check that there are no hidden loads in your code.
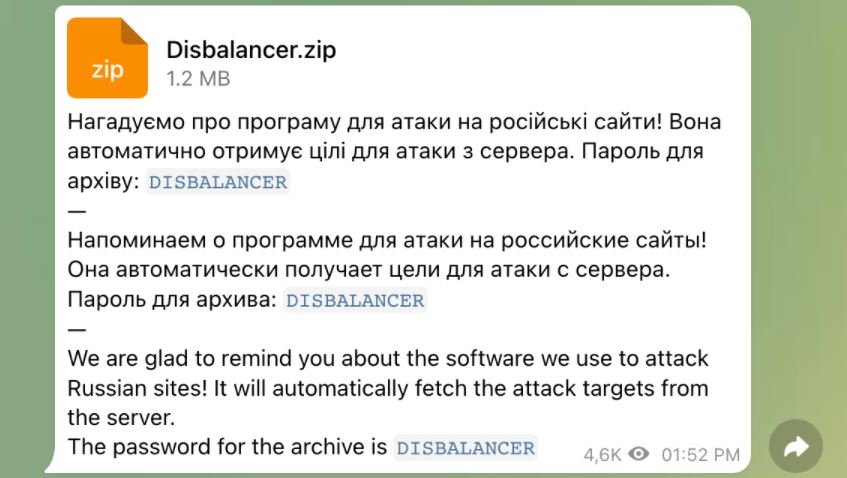
These alleged tools are also distributed through Telegram, a very popular application among Russian and Ukrainian citizens. One of the most distributed developments is Liberator, allegedly created by a hacking group known as disBalancer. This tool is described as a useful software for DoS attacks against official Russian government websites.
Although a first analysis of Liberator did not yield worrisome results, a deep review allowed identifying code of a malware for the theft of information hidden behind the tool, which in fact does work as a DoS client, which could be disastrous for an uninformed user. Liberator’s malicious payload allows threat actors to collect access credentials, cryptocurrency addresses, and authentication tokens.
Cisco Talos reports that everything starts from a malware dropper identified as Disbalancer.exe. This payload is protected with ASProtect, a well-known Windows executable packager; after installation, the malware will initiate an anti-debug check and run regsvcs.exe, which is included along with the .NET framework.
In this case, regsvcs.exe is not used as a binary, but is injected with Phoenix’s malicious code, the malware for information theft.
Researchers believe that this malware has been distributed with similar methods since the end of 2021, indicating that this is an existing operation that has made some adjustments to take advantage of the current situation. The most advisable thing for users in general would be to try to avoid the search and use of these tools, as it has been shown that this is a very effective tactic for the distribution of malware and other malicious payloads.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
