The Cisco Talos research team has detected the return of a variant of Remote Access Trojan (RAT) that in the past affected various windows system deployments, although this time they discovered that the malware is capable of affecting devices with Android operating system. Identified as LodaRAT, this Trojan has advanced capabilities for credential theft and user spying.
The report mentions that the latest version of LodaRAT includes enhanced capabilities for information theft and audio recording, and has been implemented through a hybrid user campaign in Bangladesh. Cisco Talos attributes this malicious campaign to a hacking group identified as Kasablanca.
This malware variant was first discovered in 2017, when security firm Proofpoint noted that this RAT was distributed via phishing campaigns in conjunction with the Autolt malware. This malware allows you to run all kinds of commands for audio and video recording and session hijacking. The LodaRAT variant can also steal cookies and passwords from vulnerable browsers.
Researchers note that the android version, identified as Loda4Android, is similar to RAT for Windows systems, as both include multiple functions for information collection, as well as using the same C&C server. However, the Android version of the malware is able to prevent detection, as well as capture images, read and intercept SMS messages and access call logs and contact list.
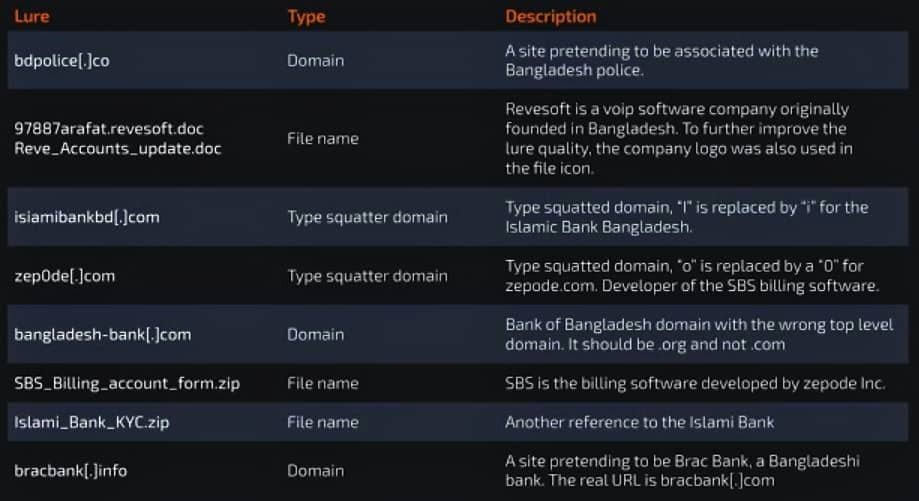
The recent increase in attacks using the new version of LodaRAT would have begun in October 2020, when threat actors launched multiple attacks on banking institutions and VoIP software providers. Researchers believe that malware developers operate in Morocco and employ a wide variety of hacking methods, including exploiting the Microsoft Office flaw tracked as CVE-2017-11182.
Android users are advised to remain alert to the danger of infection. For security, users should avoid downloading and installing apps available from unofficial sources, as this is one of the main hacking methods today. It is also recommended to ignore any email sent by unidentified users or that include malicious-looking attachments. The use of antivirus tools, antimalware and network protection tools such as firewalls and sandboxes.
To learn more about computer security risks, malware, vulnerabilities and information technologies, feel free to access the International Cyber Security Institute (IICS) website.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
