A recent report mentions that the source code of Nissan North America’s mobile apps and some internal tools have been filtered online due to a configuration error on their Git servers. According to Tillie Kottmann, a cybersecurity specialist, the compromised server had the default username and password.
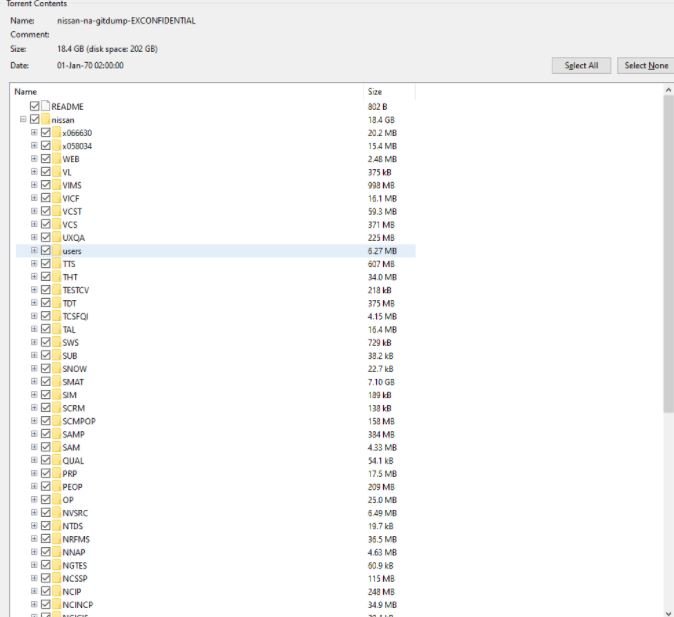
Kottmann mentions that he received the leak report thanks to an anonymous informant who asked him to notify the company of the incident. The leak involves the source code of:
- Nissan NA mobile apps
- Some details about the Nissan ASIST diagnostic tool
- Dealer portals and commercial systems
- Nissan Internal Central Mobile Library
- Nissan/Infiniti NCAR/ICAR Services
- Material for employee recruitment and customer retention
- Various marketing tools, among other confidential documents
The compromised server was disconnected yesterday after data began circulating on platforms to download torrents, hacking forums on dark web and Telegram channels. After receiving multiple requests for information, a Nissan spokesperson confirmed the incident: “We are aware of improper disclosure of some confidential details, including Nissan source code. This is a serious matter for us, we are conducting a thorough investigation.”
In May 2020, a group of researchers reported that they found a misconfigured GitLab server that filtered the source code for various Mercedes Benz applications and tools. Mercedes eventually acknowledged the incident and began work to remove the leaked information.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
