Open source interactive HTTPS proxy service Mitmproxy announced the fix of a dangerous vulnerability that would have allowed threat actors to deploy HTTP request smuggling attacks against backend servers.
These vulnerabilities exploit inconsistencies between the way intermediary and backend servers process requests in order to evade security controls, gain unauthorized access to sensitive data, and compromise other application users.
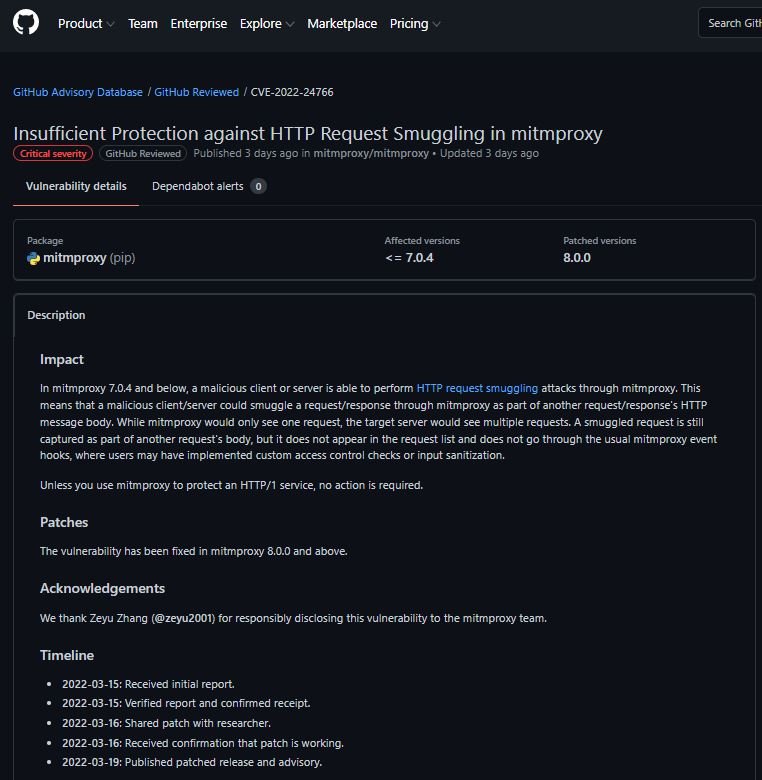
Researcher Zhang Zeyu, in charge of the report, mentioned that threat actors could smuggle requests/responses through Mitmproxy as part of the HTTP message body of another request/response. This is an obvious attack vector, although possibly for that reason it is rare currently, so the attack can prove highly successful.
In the case of Mitmproxy, an issue with the analysis of whitespace in header names resulted in a misinterpretation of HTTP headers between Mitmproxy and a downstream server: “Removing this type of vulnerability is very complicated, as different HTTP implementations are needed to agree on a common interpretation of HTTP messages,” says the Mitmproxy maintenance team.
It is possible to fix the flaw by having the proxy reject potentially malformed messages, but that would have the drawback of imposing compatibility issues with clients in real scenarios. The maintainers add that this is not a buffer overflow and there is no definitive correction, so more analysis is needed.
The error only works against the HTTP/1 services behind Mitmproxy, which currently accounts for a very small number of web servers. HTTP/2, which is the most widely used protocol today, does not rely on the use of Content-Length and Transfer-Encoding headers to determine where the body of a request ends.
Instead, a length field built into each data frame is included, and when proxies communicate with backends using HTTP/2, there is little ambiguity in the length of each message. Therefore, this particular request smuggling error would be ineffective against HTTP/2 services.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
