The developers of Travis CI, a DevOps continuous integration and continuous delivery (CI/CD) platform, recently issued a statement acknowledging the detection of a security issue, although they downplayed it.
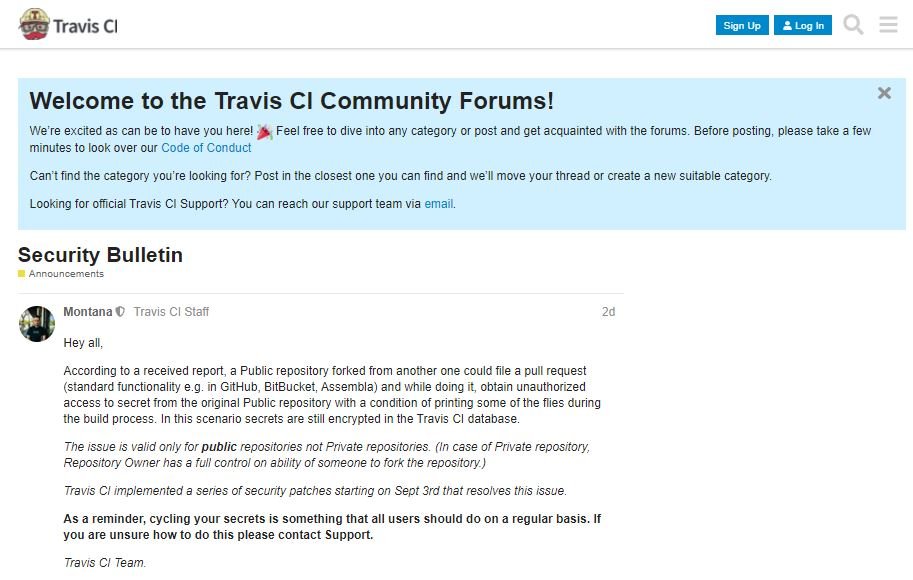
In its message, the platform notes that a forked public repository could submit a pull request (standard functionality, for example, on GitHub, BitBucket, Assembla), allowing unauthorized access to the secret of the original public repository on the condition of printing some files during the construction process.
Although the seriousness of the report was initially dismissed, arguing that the problem only affected public repositories, the cybersecurity community began to analyze the problem in depth, concluding that this error could be much more serious than previously thought.
Péter Szilágyi, cybersecurity specialist at Etherium, criticized Travis CI for dismissing such a security risk as if it were a minor issue, stating that this poses a supply chain poisoning risk for firms working with this software: “Between September 3 and 10, secure env variables from all public @travisci repositories were injected into PR [pull request] builds, signing keys, access credentials, API tokens. Anyone could exfiltrate them and deploy lateral movement attacks on thousands of potentially vulnerable organizations.”
For the expert, Travis CI was also wrong not to recognize reports of vulnerabilities in its systems or for not following incident response best practices: “Without analysis, security reports or any other protection measure, users could have been seriously exposed.”
This is a clear example of the mismanagement of incidents that characterizes software development companies, which seek to avoid public relations chaos at the cost of keeping users exposed to all kinds of security risks.
So far, Travis CI remains without answering by comments from Szilágyi and other members of the cybersecurity community, although this situation is expected to change in the coming days.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
