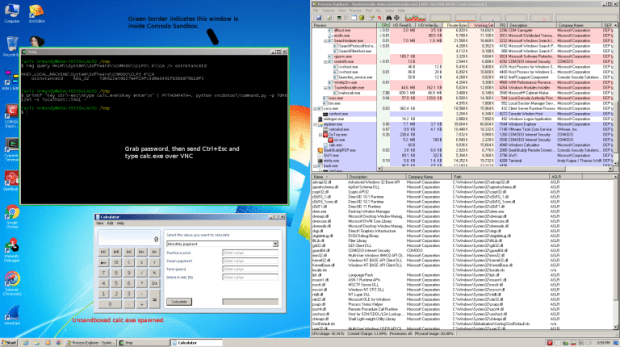
More than 8000 exposed VNC instances detected with authentication disabled belonging to critical infrastructure
Research from cybersecurity and threat intelligence company Cyble identifies a spike in attacks targeting virtual network computing (VNC) — a graphical desktop-sharing system that uses the Remote Frame Buffer (RFB)Read More →